IT Security
How hackers make entire cities collapse
Wind power stations are partially controlled via mobile phone networks. This carries risks.
Suddenly, everything collapsed. Light, television, and anything powered by electricity stopped working. The year was 2015, just before Christmas. 700,000 households in Ukraine were cut off from energy supply for several hours. They were not the only ones affected; large industrial facilities, too, found themselves in great difficulties. A blast furnace, for example, could not be shut down in a controlled manner, which resulted in serious damages. The perfidious thing was: the situation was caused deliberated by human activity. A hacker attack on the energy suppliers’ computer system was the reason.
Power grids are so-called critical infrastructures, just like water supply and transport systems. Protecting them from attacks is the objective of the German-French research project Bercom, which has been running since September 2015 and is backed by the Federal Ministry of Education and Research. The name stands for “Blueprint for a pan-European system platform for robust critical infrastructures”. Twelve project partners, including researchers from Ruhr-Universität Bochum and the Technical University of Dortmund, have joined forces for this purpose. Together, they intend to develop, for example, a secure mobile phone network. By August 2018 it should be designed for operators of critical infrastructures to be integrated into their existing communication infrastructure.
Mobile telephony as affordable and flexible alternative
One of the members of the Bochum-based team is David Rupprecht, PhD student at the Horst Görtz Institute for IT Security. He explains the reasons why mobile telephony plays such a crucial role for network providers: “In Germany, more and more wind power plants are being built, as a result of the ongoing energy revolution. The wind turbines that generate energy are scattered across large areas. In order to manage them from the control centre, operators make use of mobile telephony networks – at least for the last mile.”
Reliable monitoring of such facilities is important to, for example, maintain control over the generated energy volumes. If they are higher than the consumed energy volumes, the power grid overloads and an outage may occur, which, in turn, can paralyse communication systems. Attackers can interfere with the system by authorising surplus electricity production while overriding the system’s safety measures. The consequence would be a blackout like the one in Ukraine.

A disturbing thing is that many critical infrastructure operators currently use outdated communication technologies.
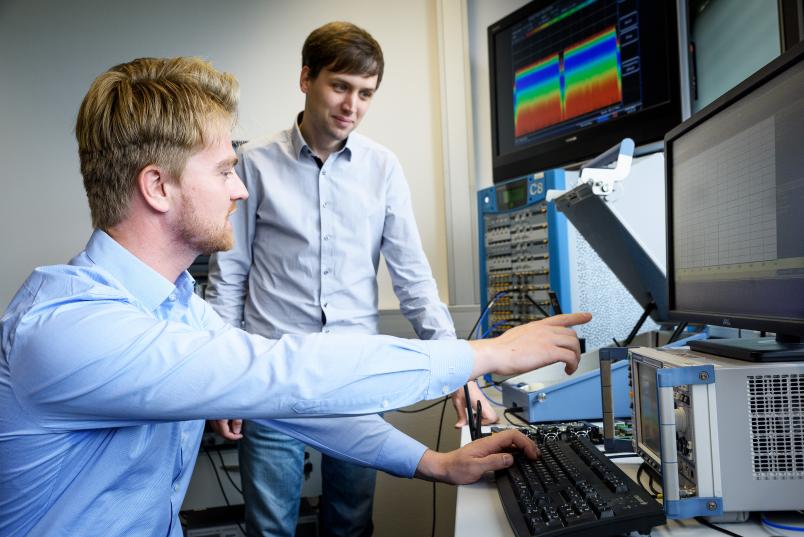
David Rupprecht
According to David Rupprecht, the disturbing thing is that many critical infrastructure operators currently use outdated and therefore insecure communication technologies such as modems or the legacy mobile phone standard GSM (Global System for Mobile Communications). In the private sector, it has long been overtaken by LTE (Long Term Evolution), the fourth-generation mobile phone standard. Compared to its predecessors, LTE is protected against a large number of known attacks, but even so it still has security vulnerabilities.
LTE as mobile phone standard of choice
The Bercom project partners are confident that they will be able to remove those vulnerabilities, thus elevating LTE to a secure mobile phone standard for the energy segment. Once it has been established in this sector, it can become useful for other critical infrastructures.
To this end, David Rupprecht has been developing tests for assessing chipsets that are installed in the control units of wind turbines to enable communication with regard to security-relevant aspects such as encryption and authentication. Encryption means that an attacker cannot access information about the system as he is unable to read the messages. Authentication means that an attacker cannot send any fake commands to the control unit as he is unable to pass himself off as a real mobile phone network. The relevant safety measures are essentially incorporated in the LTE standard, but it cannot yet be guaranteed that they are completely and correctly implemented in individual chipsets. Due to engineering tolerances, different plants might grant access to an attacker, for example permitting him to send fake messages.
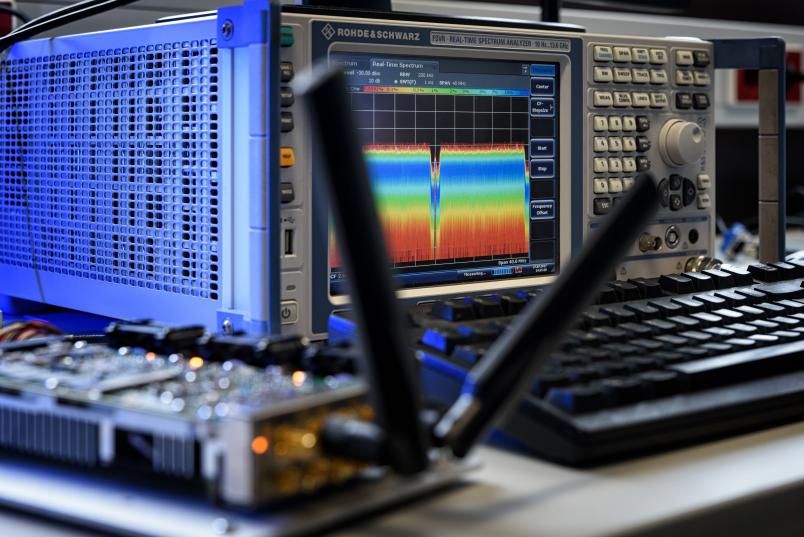
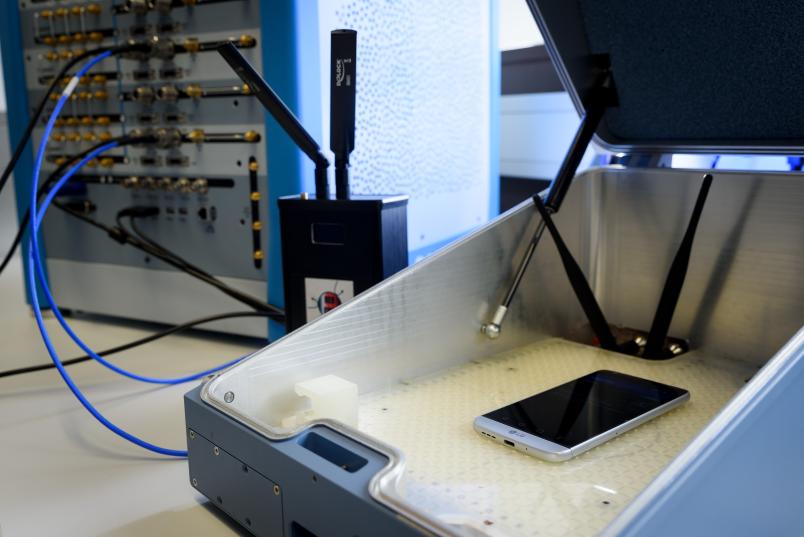
As such experiments shouldn’t be conducted in real critical infrastructures, Rupprecht carried out his tests with various mobile phones that contain the same chipsets as large plants. The PhD student from Bochum used so-called Software Defined Radios for his tests. They facilitate the sending and receiving of LTE signals. The advantage of these devices is that the signals are not processed in the hardware, as is traditionally the case, but that hardware characteristics are parametrized through software. It is precisely this property that facilitates flexible development of security tests. Consequently, Rupprecht was able to recreate an LTE base station and use it for sending non-standard compliant messages to tested chipsets. Thus, he simulated attacks on a chipset to identify vulnerabilities.
Alerts? Far from it!
The test results show: not one of the ten tested mobile phones alerted its user to an unencrypted data exchange. When it came to authentication, on the other hand, only one device failed the test; the other nine identified the fake messages and didn’t let them through. “My goal was primarily to demonstrate what the relevant tests look like and how they can be developed,” explains Rupprecht, who has already published his findings. Thus, it is possible not only to identify vulnerabilities in current chipsets, but also to render the development of future devices more secure.
One of the devices Rupprecht used for his tests was a base station, which the researchers from the Communication Networks Institute in Dortmund headed by Prof Dr Christian Wietfeld operate under shielded conditions in a lab to eliminate potential interferences. “We communicate all the time, often discussing matter on the phone and exchanging information face to face,” as he describes the collaboration. The subject matter studied by the team in Dortmund differs slightly from the one investigated by the researchers in Bochum. They try to find ways of delivering data safely, including in terms of time sensitivity, i.e. within the space of a few milliseconds. Thus, secure operation of infrastructures that rely on stable communication can be maintained at all times. Following the collaboration between the two universities, attacks on, for example, wind power plants will be rendered manageable thanks to the implementation of just-in-time countermeasures – and so will challenging situations such as natural disasters.
Collaborating in the Bercom project, David Rupprecht will have his hands full in the months to come. In the next stage, he will continue to analyse the security of components in mobile phone networks, and make sure that current and future mobile phone standards will be securely deployed in critical infrastructures.